To keep secrets off-grid and maintain your privacy, you should use encryption to turn your messages into unreadable codes that only you and your intended recipient can decode. Combine this with covert messaging techniques like steganography, which hides messages within images or audio files, making them indistinguishable from normal data. Incorporate code words to replace sensitive terms, creating layered security. Staying informed on these strategies will help you better protect your information from prying eyes.
Key Takeaways
- Combine encryption with covert messaging to protect sensitive information from interception during off-grid communication.
- Use code words to replace key terms, adding an extra layer of security in monitored environments.
- Embed secret messages within multimedia files through steganography, making detection difficult.
- Employ layered security strategies that integrate encryption, code words, and steganography for robust privacy.
- Regularly update and vet your methods to ensure maximum confidentiality and adapt to evolving threats.

In an age of constant connectivity, keeping secrets off-grid becomes essential for maintaining privacy and security. Today, digital communication channels are everywhere, making it easier than ever for outsiders to intercept sensitive information. Whether you’re sharing personal details or confidential business data, relying solely on standard methods leaves you vulnerable. That’s why mastering techniques like encryption and covert messaging is vital if you want to stay one step ahead of prying eyes.
Encryption transforms your messages into code that only you and your intended recipient can decipher. When you send a message, it’s no longer just readable text; instead, it’s scrambled into an unintelligible string. This way, even if someone intercepts your digital communication, they won’t understand the content without the decryption key. Modern encryption tools are highly effective and user-friendly, allowing you to communicate securely without needing advanced technical knowledge. Using encrypted messaging apps or email services ensures your conversations stay private, whether you’re discussing sensitive plans or personal matters.
Covert messaging takes privacy a step further by hiding the very existence of your communication. Instead of just encrypting your message, you can embed it within innocuous-looking data or images, making it difficult for outsiders to even recognize that a secret message is being transmitted. Techniques like steganography allow you to hide messages inside multimedia files, which seem ordinary to anyone without specialized tools. This approach is particularly useful in high-risk situations where even the suspicion of secret communication could lead to trouble. For example, you might encode a covert message within a seemingly normal photo or audio clip, ensuring nobody outside your circle even suspects you’re sharing sensitive information.
Using code words is another practical way to keep your secrets off-grid. Instead of explicitly mentioning sensitive topics, you substitute them with prearranged words or phrases that only your trusted contacts understand. This simple method reduces the chances of your message being misinterpreted or intercepted, especially in situations where digital communication might be monitored. Combining code words with encryption and covert messaging creates a layered defense, making it exceedingly difficult for outsiders to uncover what you’re truly discussing.
Ultimately, staying off-grid with your secrets demands a strategic approach. By leveraging encryption, covert messaging, and code words, you create multiple barriers that protect your privacy. While no method is foolproof, using these tools diligently minimizes the risks associated with digital communication. Implementing vetted security techniques ensures your secrets remain just that—secret. In an era where information is power and privacy is constantly under threat, mastering these techniques guarantees your secrets remain just that—secret.
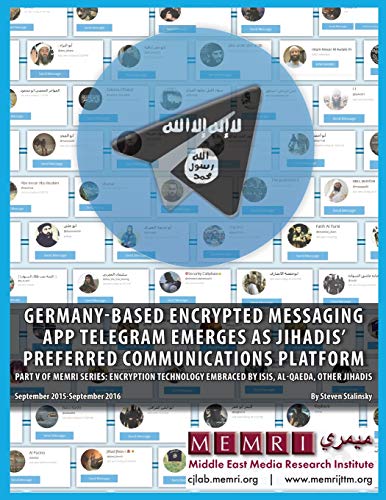
Germany-based Encrypted Messaging App Telegram Emerges as Jihadis' Preferred Communications Platform: Part V of MEMRI Series: Encryption Technology … Jihadis (September 2015 – September 2016)
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
Can Encryption Be Completely Foolproof Against Hackers?
Encryption can’t be completely foolproof against hackers because cybersecurity best practices evolve, and vulnerabilities can still exist. Hackers constantly find new ways to exploit encryption vulnerabilities, so it’s essential you stay updated on the latest security measures. While strong encryption markedly reduces risks, no system is entirely invulnerable. To protect your secrets, combine encryption with other security practices like multi-factor authentication and regular software updates.
What Are the Best Code Words for Sensitive Topics?
You should choose cultural code words that resonate within your context, making them less obvious to outsiders. Incorporate context-based ciphers to adapt your code words dynamically, ensuring they stay secure. For sensitive topics, select words that blend into everyday conversation, avoiding obvious terms. By combining cultural code words with context-based ciphers, you enhance your privacy, making it harder for anyone to decipher your messages without knowing the specific cultural or situational clues.
How Often Should Encryption Keys Be Changed?
You should change your encryption keys regularly, ideally through key rotation, to minimize risks from potential breaches. Experts recommend updating keys at least every 3 to 6 months, depending on your encryption lifespan and sensitivity of data. Frequent key rotation ensures that even if a key is compromised, the damage remains limited. Staying vigilant and adhering to best practices keeps your off-grid secrets safe and secure from unauthorized access.
Are There Legal Risks in Using Secret Codes?
Yes, there are legal risks in using secret codes. You could face legal concerns if authorities interpret your encryption or code words as signals of illegal activity, especially if laws require disclosure. Privacy implications also arise, as your coded communications might be scrutinized or requested during investigations. Always understand your local laws to avoid unintentionally violating regulations, and consider consulting legal advice when using advanced encryption or code words.
How Do I Train Myself to Recognize Covert Communication?
Recognizing covert communication is like tuning into a silent symphony; you need to listen closely. Pay attention to non-verbal cues like gestures, facial expressions, and posture, which often carry hidden messages. Contextual clues—like unusual timing or inconsistent behavior—also signal secret exchanges. To train yourself, observe interactions carefully and practice decoding patterns, gradually sharpening your awareness of subtle signals that indicate covert communication.

Hiding in Plain Sight: Steganography and the Art of Covert Communication
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
By mastering encryption and code words, you turn your secrets into a fortress, invisible to prying eyes. Think of your privacy as a delicate butterfly—easily disturbed if not carefully protected. When you stay vigilant and use these tools, you keep your off-grid life safe and sound. Remember, in the world of secrets, a well-guarded message is your strongest shield. Stay smart, stay secure, and let your privacy flourish like a hidden garden.

EASYGUARD EC002-NI-NS FSK Technology Rolling Code smart Key pke car Security Alarm System with Passive keyless Entry auto Start Stop keyless go & Touch Password Entry Backup
EASYGUARD multi-function pke car alarm system with passive keyless entry, remote start, push start, touch password entry and…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

How The *Bleep* Did You Find Me?: Real life lessons for protecting your privacy from one of America's leading skiptracers
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.